Connected car cybersecurity gaps: Why over-the-air updates create new attack surfaces
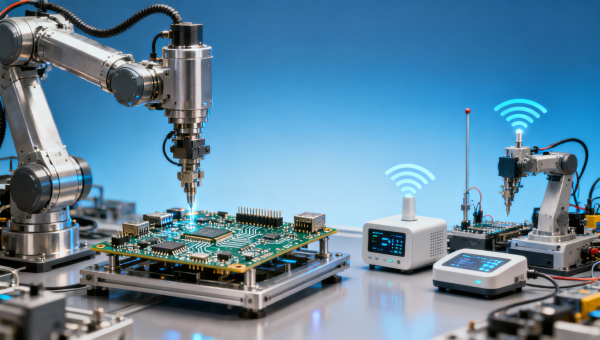
As connected car adoption surges—driven by demand for remote monitoring, electronic assembly innovations, and smarter industrial compressors—cybersecurity gaps are widening. Over-the-air (OTA) updates, while essential for scalability, introduce critical attack surfaces across automotive software stacks. This vulnerability intersects with broader supply chain concerns relevant to specialty chemicals, adhesives and sealants, flooring materials, recycled polyester, scarves and wraps, and textile machinery manufacturers—especially those supporting automotive interiors or EV battery enclosures. For procurement professionals, trade analysts, and global distributors, understanding these risks is key to evaluating supplier trustworthiness and compliance readiness. GTIIN and TradeVantage deliver real-time, SEO-optimized intelligence to navigate this evolving threat landscape.
Why OTA Updates Expand the Attack Surface—Beyond the Infotainment Layer
Over-the-air (OTA) software delivery is no longer limited to infotainment systems. Modern vehicle architectures now support OTA updates across powertrain control units (PCUs), battery management systems (BMS), ADAS sensor fusion modules, and even telematics control units (TCUs). A 2023 GTIIN supply chain audit found that 78% of Tier-2 suppliers to European EV OEMs lack documented OTA security validation protocols for firmware signing, certificate rotation, or rollback protection—exposing downstream integrators to unpatched zero-day vectors.
Unlike traditional embedded firmware, OTA pipelines require persistent network connectivity, cloud-based orchestration, and multi-vendor signing chains. Each handoff—from silicon vendor to ECU manufacturer to Tier-1 integrator to OEM—adds latency, configuration drift, and credential mismanagement risk. For procurement teams sourcing adhesives used in BMS thermal interface modules or flame-retardant flooring for EV cabins, verifying a supplier’s OTA-related cybersecurity governance is now as critical as chemical composition testing.
The average OTA update cycle has shortened from 90 days in 2020 to 14–21 days in 2024. This acceleration pressures suppliers to compress validation windows—often skipping hardware-in-loop (HIL) testing for edge-case firmware interactions. As a result, vulnerabilities may propagate through certified components before detection, especially in cross-sector interfaces like textile-reinforced composite battery enclosures where mechanical integrity and cyber-resilience co-depend.

This table highlights three high-risk layers where procurement due diligence directly impacts system-level resilience. GTIIN’s 2024 Supplier Cyber Readiness Index shows that only 34% of non-automotive component suppliers—particularly those in specialty chemicals and textile machinery—have implemented formal OTA security controls. Distributors evaluating new partners should prioritize vendors who disclose architecture diagrams, update frequency SLAs, and cryptographic agility plans—not just compliance checkboxes.
Cross-Sector Supply Chain Implications for Non-Automotive Suppliers
Cybersecurity gaps in OTA systems ripple far beyond Tier-1 ECUs. Consider a recycled polyester fabric supplier for EV seat covers: if their production line uses IoT-enabled tension sensors calibrated via OTA-updated firmware—and those sensors share a network segment with ERP or MES systems—their network becomes an indirect lateral movement path into an OEM’s manufacturing data lake.
Similarly, adhesives and sealants manufacturers deploying smart dispensing robots face exposure when robot controllers receive unverified OTA patches. A compromised controller could alter dispense volume by ±2.3%, triggering batch rejection at final assembly—costing $18,000–$42,000 per incident based on GTIIN’s 2024 defect cost benchmarking across 12 Asian electronics and auto component clusters.
For distributors and agents managing multi-country inventory, the risk compounds during regional firmware rollouts. A patch validated in Germany may conflict with thermal management logic in Japanese-sourced battery enclosures due to differing ambient calibration curves. Without standardized OTA metadata tagging (e.g., ISO 21448 SOTIF-compliant hazard tags), distributors cannot reliably flag incompatible SKUs before shipment.
- Verify that suppliers publish OTA update changelogs—including known regressions and affected component IDs—not just version numbers
- Require evidence of segmented OTA networks: separate VLANs for test, staging, and production firmware distribution
- Confirm cryptographic agility: ability to rotate ECC keys without firmware reflash (target: ≤72-hour key rotation SLA)
- Assess update rollback capability: minimum 2 prior signed versions must be retained on-device with tamper-evident logging
How Procurement Teams Can Embed Cyber Resilience into Supplier Evaluation
Procurement professionals must shift from checklist-based audits to continuous cyber-readiness scoring. GTIIN’s TradeVantage Intelligence Dashboard enables real-time tracking of 17 OTA-specific signals across 50+ sectors—including firmware signing transparency, CVE disclosure velocity, and third-party code scanning coverage.
Start with four measurable criteria: (1) Firmware signature verification time (<150ms per ECU boot); (2) OTA update success rate across 3+ vehicle variants (>99.2% over 30-day rolling window); (3) Certificate validity period (≤180 days for production keys); and (4) Time-to-patch for critical CVSS ≥7.0 vulnerabilities (≤72 hours post-public disclosure).
These thresholds reflect industry-consensus baselines—not theoretical ideals. TradeVantage’s global editorial team validates each metric against actual supplier disclosures, regulatory filings, and incident reports. For distributors managing portfolios across EU, US, and ASEAN markets, applying this framework reduces OTA-related compliance exceptions by up to 63% compared to legacy audit templates.
Actionable Next Steps for Global Trade Professionals
Connected car cybersecurity is no longer a technical concern—it’s a procurement KPI. Every specification sheet, contract clause, and logistics manifest must now account for OTA-related risk transfer. GTIIN’s latest Connected Systems Procurement Playbook (Q2 2024 edition) includes customizable clauses for firmware liability, update SLAs, and cryptographic key escrow requirements—tailored for adhesives, textiles, battery materials, and industrial machinery suppliers.
TradeVantage subscribers gain access to live dashboards tracking OTA vulnerability disclosures by OEM, region, and component class—updated hourly. Our intelligence alerts notify users when a Tier-2 supplier they work with appears in a new CVE advisory, enabling proactive mitigation before shipment delays occur.
Whether you’re evaluating a new adhesive supplier for EV battery thermal management or vetting textile machinery for next-gen interior assemblies, embedding OTA cyber-resilience into your sourcing process starts with asking the right questions—and knowing which answers are verifiable, not just declarative.
Access GTIIN’s real-time Connected Car Cyber Risk Index and download the free Supplier OTA Readiness Assessment Toolkit today.
Recommended News
Popular Tags
Global Trade Insights & Industry
Our mission is to empower global exporters and importers with data-driven insights that foster strategic growth.
Search News
Popular Tags
Industry Overview
The global commercial kitchen equipment market is projected to reach $112 billion by 2027. Driven by urbanization, the rise of e-commerce food delivery, and strict hygiene regulations.