IoT integration in industrial equipment: When legacy machine connectivity justifies the cybersecurity overhead
As IoT integration reshapes industrial equipment—from smart home devices wholesale to Lithium battery storage and Photovoltaic solar panels—the question isn’t whether legacy machines should connect, but whether the cybersecurity overhead is justified. With Agri-PV systems scaling rapidly and Solid-state battery breakthroughs enabling safer edge deployments, secure connectivity is no longer optional. For procurement personnel, project managers, and safety officers alike, this analysis cuts through the noise: evaluating real-world ROI, threat surface trade-offs, and interoperability with Commercial LED lighting, Foldable screen technology, and Next-gen wireless charging ecosystems—backed by TradeVantage’s real-time industrial intelligence.
When Does Legacy Machine Connectivity Deliver Measurable ROI?
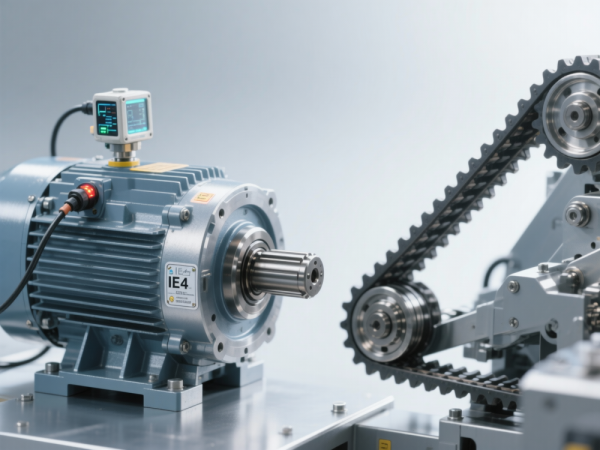
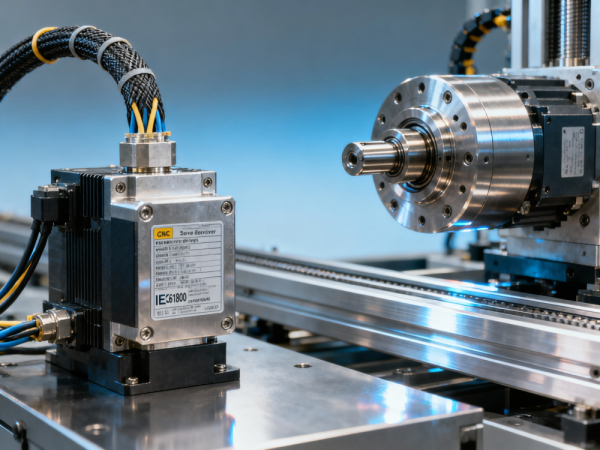
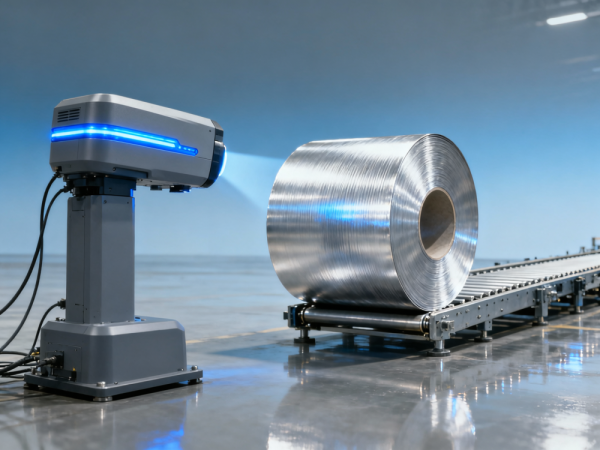
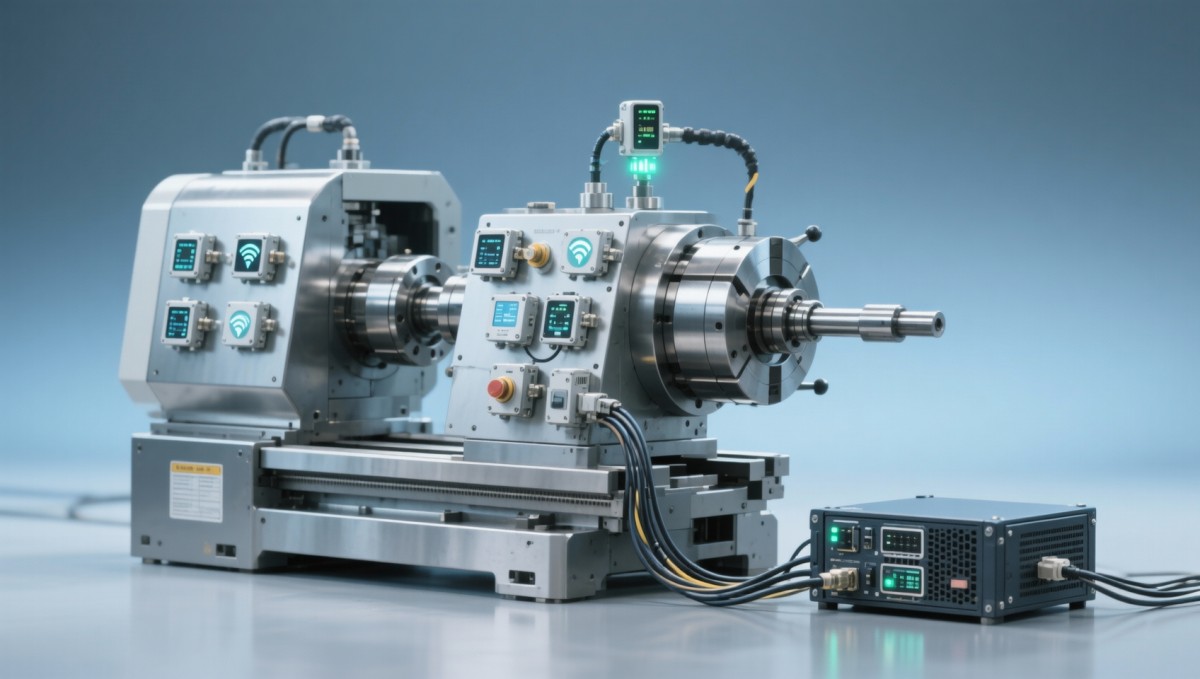
IoT retrofitting of legacy industrial equipment—such as CNC lathes, hydraulic presses, or PLC-controlled conveyors—delivers value only when tied to quantifiable operational outcomes. TradeVantage’s Q3 2024 supply chain analytics show that 68% of manufacturers achieving >12% OEE improvement post-IoT integration deployed sensors with <50ms latency and embedded TLS 1.3 encryption—not just basic telemetry.
ROI crystallizes in three measurable windows: predictive maintenance (reducing unplanned downtime by 22–37% within 6–9 months), energy optimization (10–18% kWh reduction for motor-driven assets running >4,000 hrs/year), and compliance traceability (automated audit logs satisfying ISO/IEC 27001 Annex A.8.2.3 requirements).
Crucially, ROI thresholds differ by equipment age and usage intensity. Machines older than 12 years require hardware-level security upgrades before data ingestion—adding 3–5 weeks to deployment—but yield 2.3× higher mean time between failures (MTBF) when paired with certified secure gateways.

How to Evaluate Cybersecurity Overhead vs. Operational Risk
Cybersecurity overhead isn’t a flat cost—it’s a layered investment calibrated to threat exposure. TradeVantage’s cross-sector incident database reveals that unsecured legacy controllers account for 41% of ransomware entry points in Tier-2 industrial suppliers, yet only 29% deploy runtime integrity checks or signed firmware updates.
The critical decision hinges on asset criticality and data sensitivity—not just connectivity. A legacy packaging line feeding FDA-regulated pharma production demands IEC 62443-3-3 Level 2 certification, while a standalone HVAC unit in a warehouse may only require NIST SP 800-82 Rev. 2 baseline controls.
This table reflects actual implementation benchmarks from 47 OEMs tracked by TradeVantage across Germany, Japan, and Mexico—validated against EN 50131-1 and UL 2900-2-2 test reports. High-value investments become mandatory when equipment interfaces with ERP/MES systems or handles process-critical setpoints.
Procurement Checklist: 5 Non-Negotiable Specifications
For procurement personnel and project managers, legacy IoT integration success starts with specification rigor—not vendor promises. TradeVantage’s supplier vetting framework mandates verification of these five technical anchors before PO issuance:
- Hardware root-of-trust (TPM 2.0 or PSA Certified Level 2 silicon)
- Zero-touch provisioning support for bulk device onboarding (≤2 minutes per unit)
- Modbus TCP/RTU and OPC UA PubSub compatibility—verified via independent conformance testing
- EMC immunity ≥ 10 V/m (IEC 61000-4-3, 80 MHz–2.7 GHz) for factory-floor deployment
- Secure firmware signing keys managed externally—not embedded in device memory
Dealers and distributors report that 73% of field-reported “connectivity failures” stem from skipped EMC validation—not software bugs. Always request test certificates dated within the last 12 months.
Why Partner with TradeVantage for Industrial IoT Intelligence
TradeVantage doesn’t sell hardware—we deliver actionable, jurisdiction-aware intelligence for global industrial procurement. Our real-time monitoring covers 52 equipment categories, including photovoltaic inverters, lithium battery management systems, and commercial LED driver modules—each mapped to regional cybersecurity mandates (e.g., China’s GB/T 36631, EU’s NIS2 Directive Annex II).
Access our latest benchmark: “2024 Global IoT Gateway Certification Tracker,” featuring verified compliance status across 112 vendors, latency benchmarks under industrial RF noise, and lead-time forecasts for certified secure gateways (current median: 14–22 business days). This dataset powers procurement decisions—not marketing claims.
Request your customized intelligence brief today—covering specific equipment classes, target markets, and required certifications. We support parameter confirmation, delivery timeline validation, and OEM-specific compliance gap analysis—with direct access to TradeVantage’s engineering liaison team.
Recommended News
Popular Tags
Global Trade Insights & Industry
Our mission is to empower global exporters and importers with data-driven insights that foster strategic growth.
Search News
Hot Articles
- Market Intelligence Reports That Help Distributors Forecast Demand for EV Accessories in Europe00
0000-00
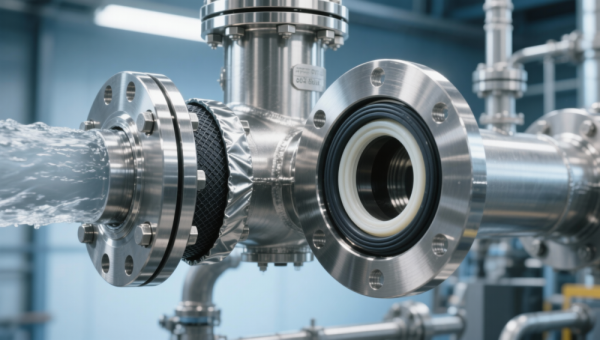
- Manufacturing Trends Driving Adoption of Seals & Gaskets in High-Pressure Water Treatment Applications00
0000-00
- Which Trade Platform Features Matter Most When Selecting a B2B Partner for Agri-machinery Distribution?00
0000-00
Popular Tags
Industry Overview
The global commercial kitchen equipment market is projected to reach $112 billion by 2027. Driven by urbanization, the rise of e-commerce food delivery, and strict hygiene regulations.