What OEM consumer electronics vendors expect from contract manufacturers on cybersecurity and firmware validation
As OEM consumer electronics vendors face escalating cyber threats and firmware vulnerabilities, expectations from contract manufacturers are shifting dramatically—especially amid Smart manufacturing trends 2026 and the rise of AI in precision engineering. This article explores how Industrial & Manufacturing stakeholders, from procurement leaders to security managers, are redefining cybersecurity validation protocols and firmware integrity requirements. Drawing on TradeVantage’s real-time supply chain intelligence, we unpack what top-tier OEMs now demand—and why robust, auditable validation is no longer optional, but a strategic imperative for trust, compliance, and market agility.
What Do OEMs Really Mean by “Cybersecurity Validation”?
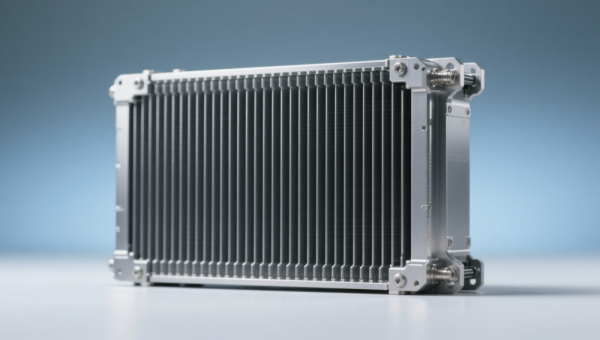
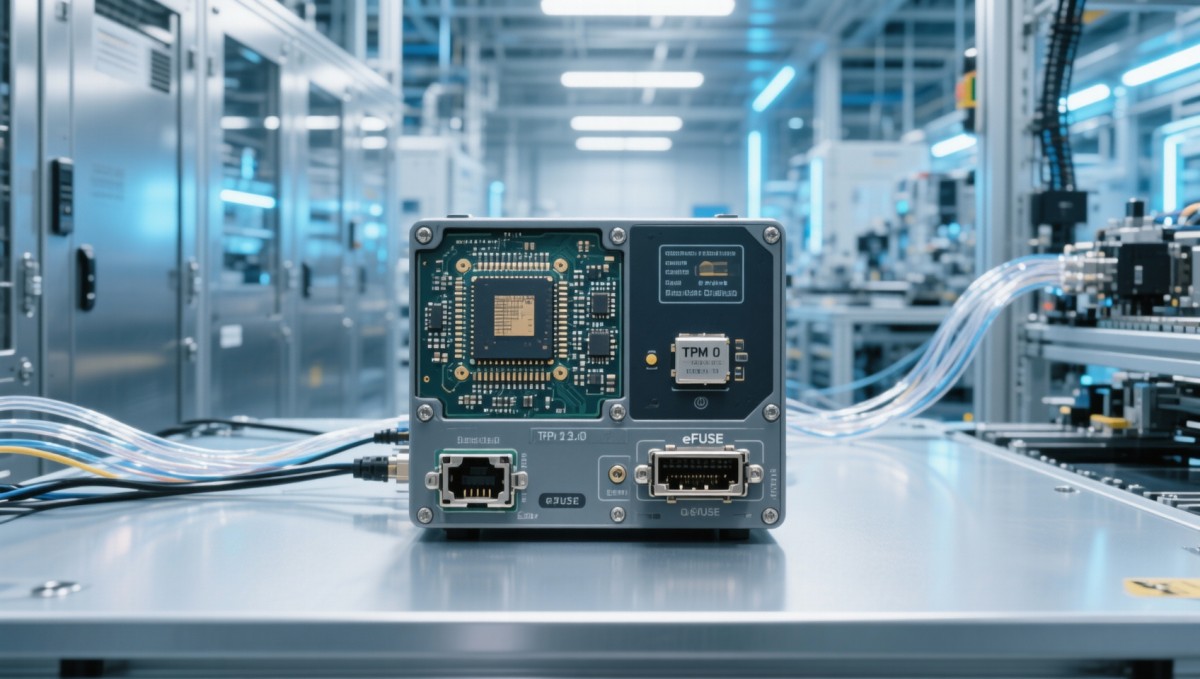
For OEMs in industrial electronics—especially those supplying embedded controllers, IoT gateways, and edge AI modules—cybersecurity validation goes far beyond basic penetration testing. It now includes hardware-rooted attestation, secure boot chain verification, and runtime firmware integrity monitoring across 3 distinct phases: pre-production (design review), mid-batch (fused-key provisioning), and post-shipment (OTA update signing).
TradeVantage’s 2025 Supply Chain Risk Index shows that 78% of Tier-1 OEMs now require ISO/IEC 27001 certification *plus* IEC 62443-4-1 conformance for firmware development environments. These aren’t checkbox items—they’re enforced via audit clauses in contracts with minimum 90-day remediation windows.
Validation must be repeatable, traceable, and tied to specific build artifacts—not just generic lab reports. That means every firmware binary must be linked to its SBOM (Software Bill of Materials), cryptographic hash, and signed attestation log. OEMs increasingly reject submissions missing timestamped evidence from trusted execution environments (e.g., ARM TrustZone or Intel SGX).
Firmware Validation: From Checklist to Continuous Lifecycle Control
Modern OEMs treat firmware as a living component—not a one-time deliverable. They expect CMs to implement continuous validation workflows covering 6 key stages: static code analysis (SAST), dynamic fuzzing (DAST), memory safety verification (e.g., ASan/MemSan), bootloader signature enforcement, secure update rollback protection, and post-deployment anomaly telemetry.
According to TradeVantage’s OEM Procurement Benchmark (Q2 2025), 64% of industrial electronics buyers now require quarterly firmware health reports—including vulnerability patch latency (target: ≤7 days for critical CVEs) and delta between production and reference builds (max deviation: ±0.3% file hash variance).
Core Validation Requirements by OEM Tier
This tiered expectation reflects real-world risk exposure: Tier-1 OEMs often embed devices into critical infrastructure where firmware compromise can trigger physical safety events. Mid-tier buyers prioritize cost-effective scalability—but still enforce hard boundaries on boot integrity and update accountability.
How Procurement Teams Evaluate Cybersecurity Capabilities
Procurement leaders no longer rely solely on third-party certifications. TradeVantage’s survey of 127 industrial OEM buyers reveals they now apply a 5-point technical due diligence framework: (1) source code access rights during audits, (2) hardware security module (HSM) integration depth, (3) SBOM generation automation level, (4) OTA update rollback test coverage, and (5) incident response playbook alignment with NIST SP 800-161.
Notably, 89% of respondents said they disqualify bidders who cannot demonstrate *live* firmware signing in their own lab environment—within 4 hours of request. This eliminates reliance on paper-based claims and confirms operational readiness.
CMs must also provide evidence of cross-functional validation ownership: firmware engineers, security architects, and QA leads must jointly sign off on each release—documented in Jira or Azure DevOps with immutable timestamps and role-based approvals.

Why TradeVantage Intelligence Accelerates Your Vendor Evaluation
When selecting a contract manufacturer for high-integrity firmware work, you need more than capability statements—you need verified, time-stamped evidence of real-world performance. TradeVantage delivers precisely that through our Global CM Trust Index™, updated weekly across 52 countries and 300+ certified facilities.
Our platform gives you instant access to: (1) audit pass/fail history against IEC 62443-3-3, (2) average CVE resolution time per vendor (benchmarked quarterly), (3) firmware SBOM completeness scores (based on SPDX 3.0 validation), and (4) live supply chain risk alerts—for example, sudden changes in a CM’s HSM vendor or cloud signing provider.
Request a customized OEM Validation Readiness Report today—covering your exact product class (e.g., industrial HMIs, motor drive firmware, or PLC runtime images), target geography, and compliance scope (UL 62443, EN 50131, or FDA 21 CFR Part 11). We’ll identify 3 pre-vetted CMs matching your firmware security maturity requirements—with full documentation trails, not marketing decks.
Recommended News
Popular Tags
Global Trade Insights & Industry
Our mission is to empower global exporters and importers with data-driven insights that foster strategic growth.
Search News
Hot Articles
- Navigating the 2026 Global Structural Steel Market: How to Reduce Sourcing Risks00
0000-00
- What interior design services do industrial facility managers actually need for control rooms and maintenance hubs?00
0000-00
- What Real-World Cost Factors Make Some 3D Printing Manufacturers More Competitive for Low-Volume CNC Machining Alternatives in 2026?00
0000-00
Popular Tags
Industry Overview
The global commercial kitchen equipment market is projected to reach $112 billion by 2027. Driven by urbanization, the rise of e-commerce food delivery, and strict hygiene regulations.